Research
I have developed a strong research potential in innovative physical layer security solutions for future wireless technologies with ultra-low energy requirements but high security standards. My research aims to bridge the gap between the theoretical modelling and practical exploitation of physical layer security using state-of-the-art testbeds and equipment.
Research Keywords
Research Topics
My research aims to exploit the wireless channel for security and sensing.
1. Wireless Security
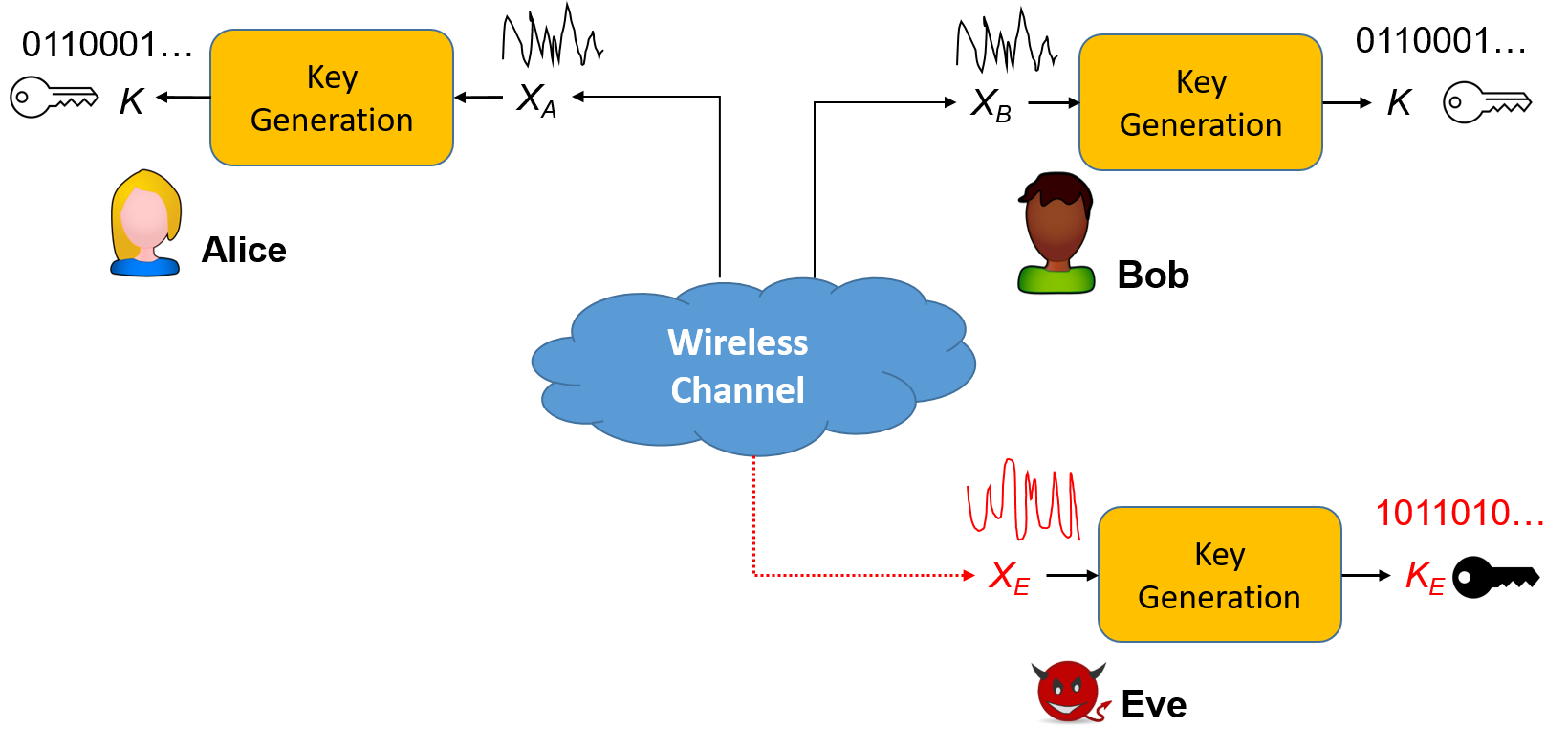
Secure communication will be achieved by using key generation and device authentication. They are key techniques for physical layer security. Please visit Physical Layer Security for a recommended reading list.
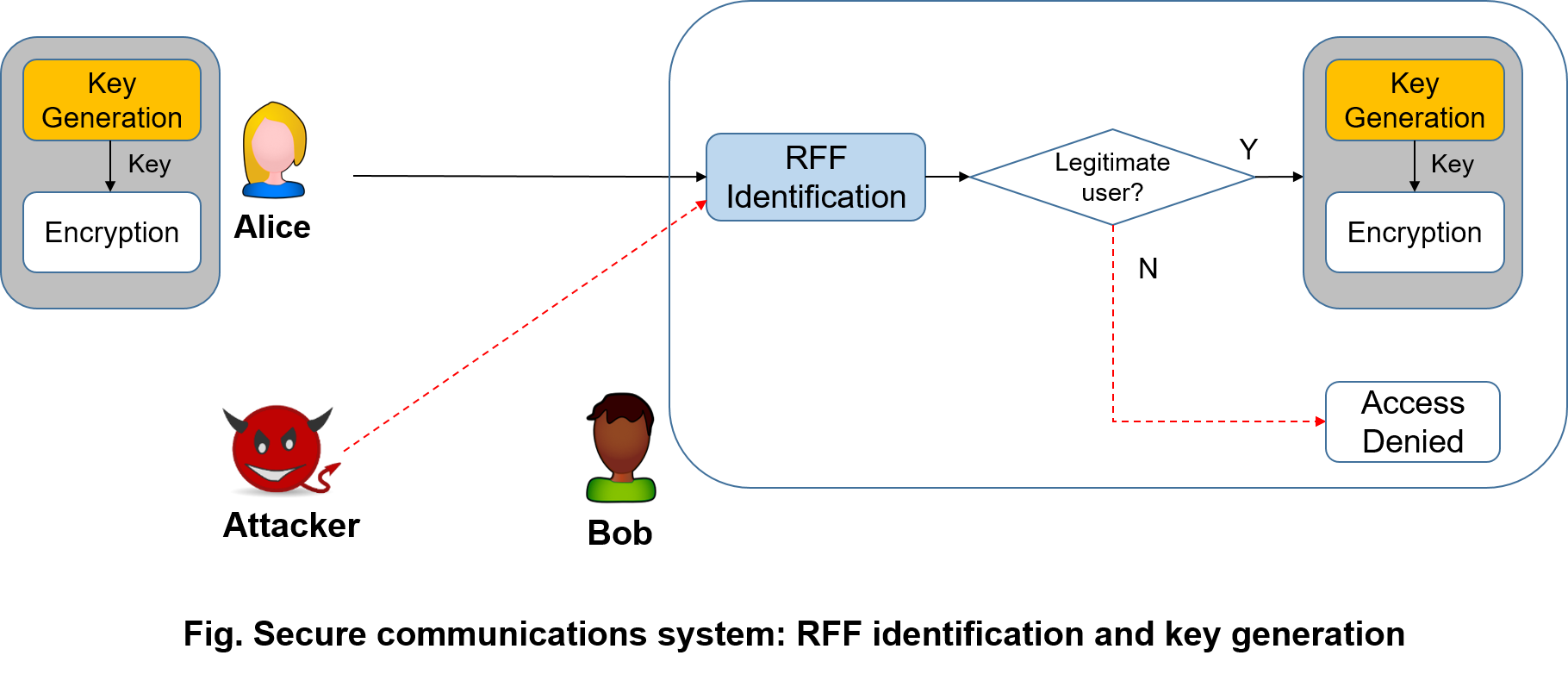
1.1 Key Generation from Wireless Channels
Key generation is an emerging technique to establish cryptographic keys between legitimate users by extracting randomness from their common channels.
- Key Generation Overview
- Key Generation Recommended Reading
- Key Generation Dataset
- Key Generation Publication at University of Liverpool
- Key Generation Projects
- Key Generation Demonstration using WARP
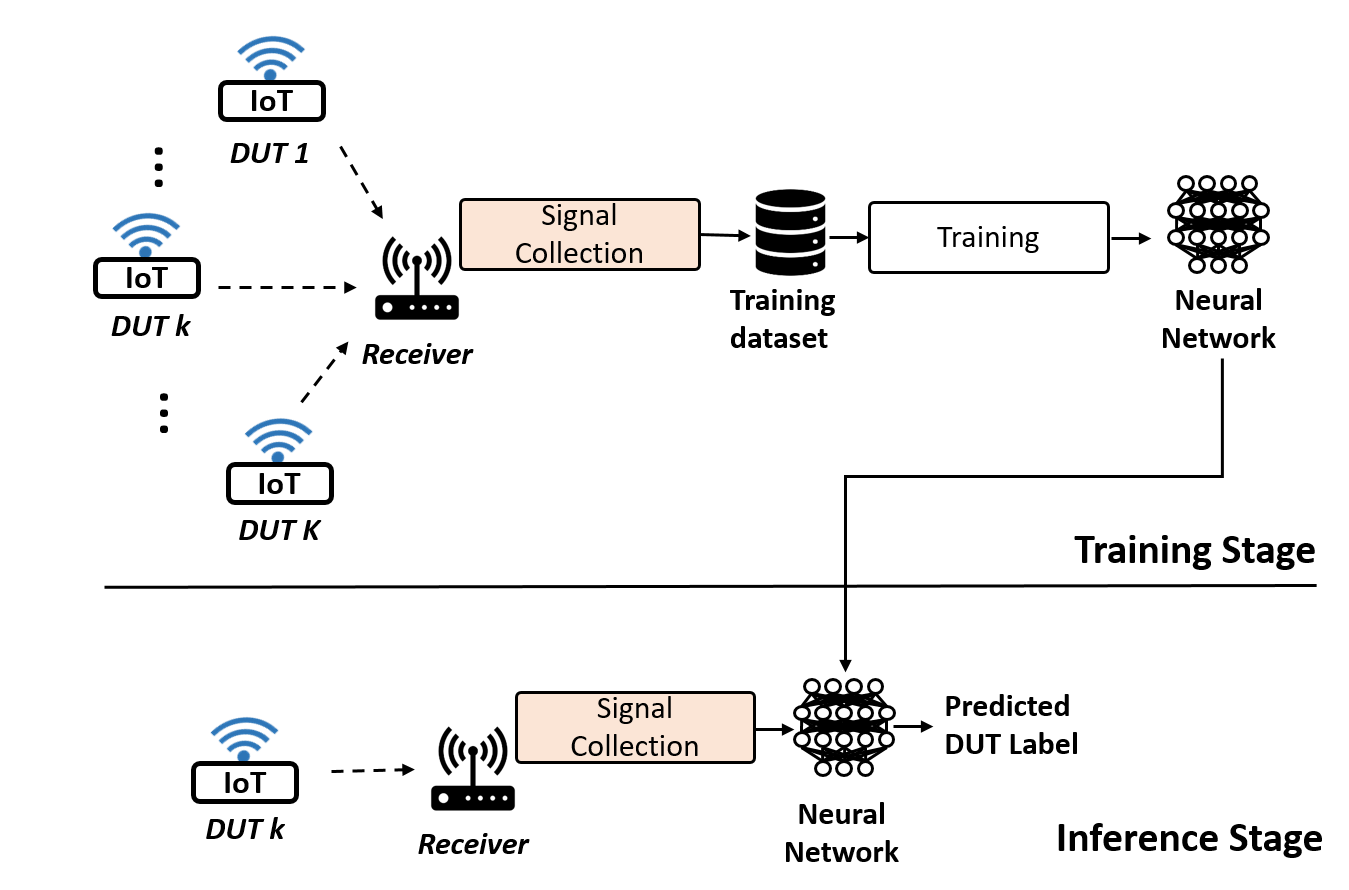
1.2 Radio Frequency Fingerprint Identification (RFFI)
All the components of wireless devices will have slightly different features, e.g., carrier frequency of the oscillators, from the manufacturing processing. Similar to biometric fingerprint, these characteristics are unique and permanent, which can act as the fingerprint of the devices. This technique first requires collecting the device fingerprint and storing them in a database, and then classifies devices by comparing with the stored database whenever a device wishes to join the network.
- RFFI Overview
- RFFI Recommended Reading List
- RFFI Dataset
- RFFI Resources
- RFFI at University of Liverpool
- RFFI at University of Liverpool (By Topics)
- How to Construct an RFFI System
- RFFI Projects
1.3 Physical Layer Authentication
- Physical Layer Authentication Overview
- Physical Layer Authentication Recommended Reading List
- Physical Layer Authentication Dataset
- Physical Layer Authentication Resources
- Physical Layer Authentication at University of Liverpool
2. Wireless Sensing
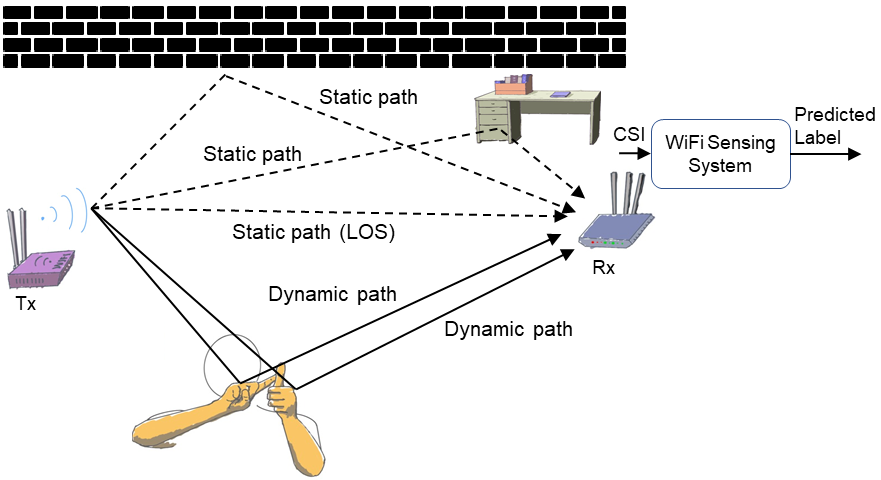
2.1 Wi-Fi Sensing
- Wi-Fi Sensing Overview
- Wi-Fi Sensing Recommended Reading List
- Wi-Fi Sensing Dataset
- Wi-Fi Sensing Resources
- Wi-Fi Sensing at University of Liverpool
2.2 mmWave Radar Sensing
To be updated
Research Demonstration
We are always keen to apply our knowledge to practical applications. Hence we have created several demonstration videos to present our applied research.
Radio Frequency Fingerprint Identification
- Wi-Fi RFFI Demonstration
- RFFI LoRa Demonstration
- Deep Learning-Powered Radio Frequency Fingerprint Identification for LoRa
Key Generation
- Wi-Fi Key Generation Demonstration using WARP
- Wi-Fi Key Generation Demonstration using Raspberry Pi
- Heartbeat Key Generation Demonstration Using PPG Sensors
Internet of Things (IoT)
Resources and Facilities
We are equipped with abundant wireless devices including software defined radios, wireless kits, GPU platform etc. Please visit Resources and Facilities for detailed information.
Research and Technical Resources
Please visit Research and Technical Resources for detailed information.